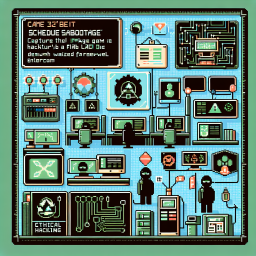
A backup server hums quietly, running its automated maintenance tasks on schedule. But are those scheduled tasks really secure? SSH in, enumerate the system like a real pentester, and discover how a simple misconfiguration can lead to complete system compromise. Time is ticking, the cron job runs every minute!
Linux privilege escalation through misconfigured cron jobs is one of the most common attack vectors discovered during penetration testing engagements. Cron is the time-based job scheduler in Unix-like operating systems, used to automate repetitive tasks such as backups, log rotation, and system maintenance. When cron jobs are configured with improper file permissions or run scripts that can be modified by unprivileged users, they become a direct path to root access.
How Cron Job Exploitation Works
Cron jobs execute commands or scripts at predefined intervals, often running with root privileges to perform system-level tasks. The vulnerability arises when a script executed by a root-owned cron job is writable by a lower-privileged user. By modifying the script content, an attacker can inject arbitrary commands that will be executed with root permissions the next time the cron job runs. This is a classic example of a time-of-check to time-of-use (TOCTOU) vulnerability in system administration.
Enumeration Techniques for Cron Jobs
Discovering exploitable cron jobs requires systematic enumeration of the target system. Security professionals examine /etc/crontab, user-specific crontabs in /var/spool/cron/, and cron directories like /etc/cron.d/, /etc/cron.daily/, and similar paths. Beyond reading cron configurations directly, monitoring tools like pspy can detect processes spawned by cron without requiring root access. File permission analysis on scripts referenced by cron entries reveals whether modification is possible.
Why This Matters for System Security
Cron job misconfigurations are prevalent in real-world environments because system administrators often prioritize functionality over security when setting up automated tasks. Backup scripts, maintenance routines, and monitoring tools frequently run with elevated privileges while residing in directories with overly permissive access controls. Understanding Linux privilege escalation through scheduled tasks is essential for both offensive security professionals conducting penetration tests and defensive teams hardening their infrastructure against unauthorized access.
What You Will Learn
- Learn systematic Linux file system enumeration techniques
- Understand how cron jobs work and how to identify misconfigured scheduled tasks
- Analyze file permissions to find security weaknesses in automated scripts
- Practice privilege escalation through writable cron job scripts
- Develop SSH-based remote access and system navigation skills
- Recognize common system administration mistakes that lead to privilege escalation
Prerequisites
Ready to hack this lab?
Create a free account and start practicing cybersecurity hands-on.
Start Your Challenge
New here? Here's what to do
Ready to hack this lab?
Create a free account to start your own dedicated server, submit flags, and earn XP on the leaderboard.
Start Hacking Free